For privacy reasons YouTube needs your permission to be loaded.
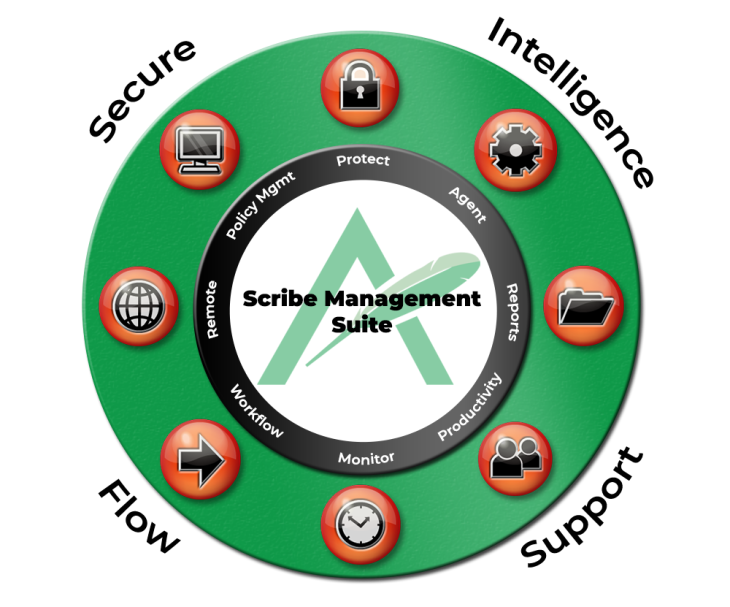
I AcceptTHE ARMARIUS SCRIBE MANAGEMENT SUITE
Customize & Conquer
Armarius’ Scribe Management Suite offers a flexible range of capabilities configurable to meet your data and security needs. Combine any of the four feature areas to create an efficient, no-frills plan that works for you.
For privacy reasons YouTube needs your permission to be loaded.
I AcceptTested and Proven
USER-LEVEL DATA PROTECTION
FOR PROACTIVE PROTECTION
Your organization relies on sensitive data, so you need no-compromise data protection for your remote work from home employees. Cloud-delivered for reduced complexity, cross-platform coverage for zero gaps, and flexible controls to align with your risk profile